Cyber GRC for Energy Trading: Building a CISO-Ready Governance Framework
A practical governance, risk, and compliance framework purpose-built for energy trading environments.
 Roy Castillo
October 2025
8 min read
Roy Castillo
October 2025
8 min read
Energy trading organizations face a unique cybersecurity governance challenge: they must satisfy multiple, overlapping regulatory frameworks while protecting both IT systems that process billions in transactions and OT systems that control physical infrastructure. This article presents a practical GRC framework built for this complexity.
The GRC Challenge in Energy Trading
Energy trading organizations sit at the intersection of financial regulation (SOX, Dodd-Frank), critical infrastructure security (NERC CIP, TSA Directives), data privacy (CCPA, GDPR), and industry standards (NIST CSF, IEC 62443). Each framework has its own requirements, assessment cycles, and reporting obligations.
Most organizations manage these frameworks independently — separate teams, separate tools, separate assessment processes. This creates redundant effort, inconsistent risk evaluation, and governance gaps where frameworks don't overlap.
A Unified GRC Architecture
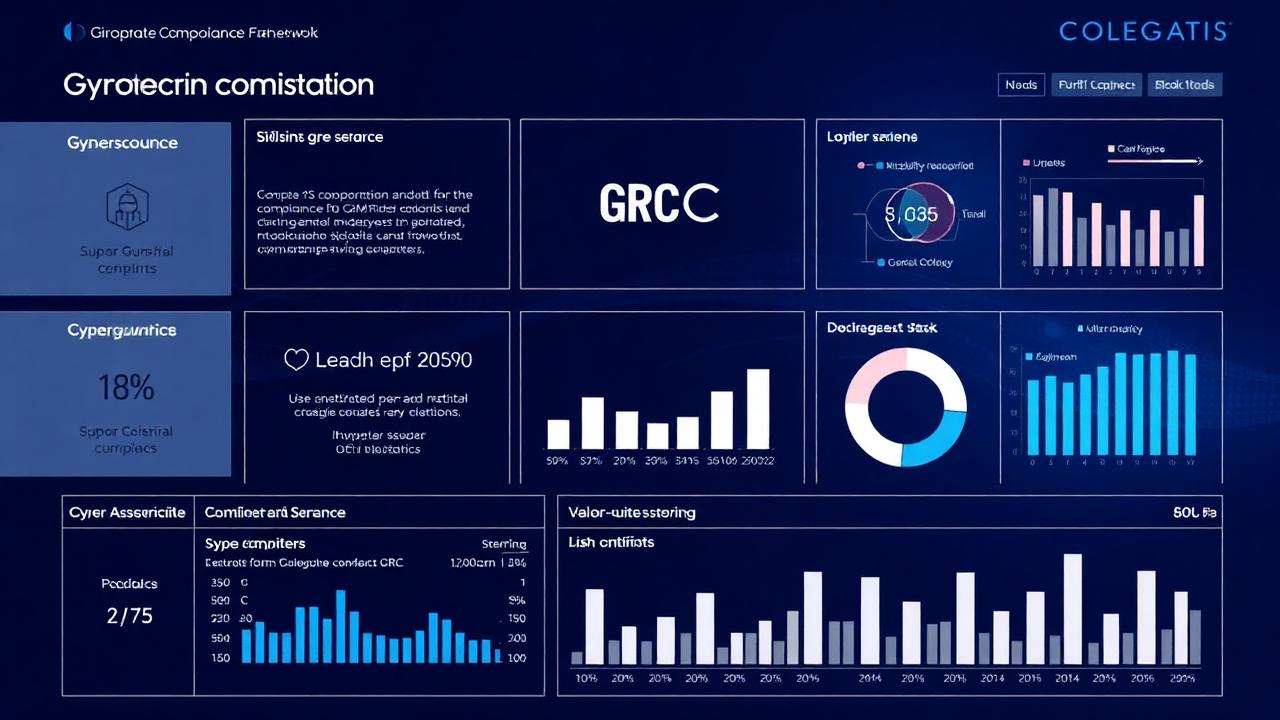
An effective GRC framework maps all regulatory requirements to a unified control catalog, then implements and monitors those controls once while reporting against multiple frameworks. The control catalog should align with NIST CSF as a common framework, with mappings to each specific regulation.
This approach reduces assessment effort by 40-60% while improving coverage and consistency. It also enables risk-based prioritization across frameworks — instead of treating every requirement equally, you can focus resources on the controls that address the highest-risk areas.
"Energy trading organizations with unified GRC frameworks spend 50% less time on compliance assessments while achieving higher compliance scores."
Risk Quantification for Energy Operations
Traditional risk assessment produces qualitative ratings (high/medium/low) that don't translate into business terms. Modern GRC requires quantitative risk analysis that expresses cyber risk in financial terms — expected annual loss, impact on trading operations, and cost of remediation.
For energy trading organizations, this means modeling scenarios specific to their operations: ransomware impacting trading systems during peak demand, data breach exposing counterparty positions, OT compromise disrupting physical deliveries. Each scenario should be quantified in terms of financial impact and probability.
Continuous Compliance Monitoring
Point-in-time assessments are necessary but insufficient. Between assessments, configurations drift, new vulnerabilities emerge, and controls degrade. Continuous compliance monitoring — automated scanning against control requirements — provides ongoing assurance between formal assessments.
Implement automated controls testing for technical controls (access management, patching, configuration), with human verification reserved for process and governance controls. Dashboard visibility into compliance status should be available to the CISO and board risk committee.
Ready to implement these strategies?
Our team can help you assess your current capabilities and build a roadmap tailored to your operations.
Request a ConsultationRelated Articles

OT Cybersecurity Framework for Energy Infrastructure: Beyond TSA Compliance
Pipeline SCADA Cybersecurity: A Step-by-Step Guide to TSA Security Directive Compliance